🔑 Password attack types and mitigation strategies
In this post we are going to talk about different password attacks. Knowing how to attack it will help us to propose a defense solution.
In general there is 2 main ways we can get a username and a password. We can either guess them or steal them. Before we begin we also need to keep in mind that sometimes an attacker have a concrete username in mind they want to get the access to and sometimes the username doesn't matter, the attacker wants to gain the access to the service under any account. For example to use a service for free, depleting the balance of the victim.
The state of the art mitigation strategy for the following attacks is hardware-based Multi-Factor Authentication (MFA) but the vast majority of the attacks can be stopped with Software MFA.
Bruteforce attack
Bruteforce is the most easy-to-setup and least effective of the attacks for a typical login form. We start by trying each and every permutation of the password until we land on the one that lets us in. It is unpractical because even if we are trying to guess a 6-character password consisting of just lower-case letters we would have to go through 26^6 = 308,915,776 permutations. Needless to say for the bruteforce attack to work the form needs to come back with the result within milliseconds, otherwise the attack quickly starts to take more than a lifetime. If the form doesn't disallow repeated failed attempts, this method might be effective in case we are trying to guess a short string. For example a 4-digit pin, as it only allows 10^4 = 10,000 permutations.
Bruteforce attack mitigation
The following 2 strategies are proven to be relatively effective:
- Limiting the number of failed attempts from a single IP
- Slowing down password matching
Dictionary attack
To speed up the process as an attacker we can use the list of most common passwords. This article shows the following breakdown:
0.5% of users use the word password
0.4% use password or 123456
0.9% use either password, 123456 or 12345678
1.6% use a password from the list of top 10 passwords
4.4% use a password from the top 100 passwords
9.7% use a password from the top 500 passwords
13.2% use a password from the top 1,000 passwords
30% use a password from the top 10,000 passwords
🤯
I wouldn't believe it if I didn't see it myself, granted the numbers are lower for business accounts versus consumer ones. Think about it for a second: almost 3rd of all users on a given service have a password that can be guessed in under 10,000 iterations.
Considering how many services are out there an attacker can simply create a bot that would try to opportunistically login into all of them using a relatively low set of passwords.
Dictionary attack mitigation
Mitigations such as rate limiting is an effective way to fight against dictionary attacks.
The easiest way to mitigate the attack is to disallow users to use a password from the list of top passwords.
Credential stuffing attack
Credential stuffing exploits password reuse. Users tend to use the same password on multiple websites, so a breach of one of them can lead to the credentials being stolen and applied to other. The principle is very simple: an attacker obtains the list of stolen credentials and tries them on all the services out there.
To learn more about data breaches I suggest checking out [Have I Been Pwned] (https://haveibeenpwned.com/). It's the best resource on the subject.
Credential stuffing attack mitigation
With a perfect dataset an attacker can gain the access to an account in a single try. sometimes they try to compromise a few accounts from a single IP.
To protecting against credential stuffing we need to store a giant dataset of breached credentials, which is not always cheap. These datasets can take up to tens of GB of data. However, it's well worth the hustle for a reputable service.
Phishing attack
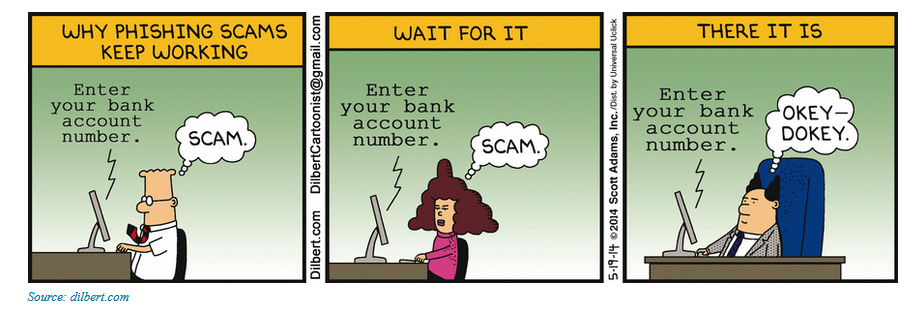
To stage a phishing attack we need to craft a message that would look like the one coming from the website we wish to compromise. An attacker also needs to host a form identical to the one an the original website.
An email asking to perform an urgent action is one of the most common approaches. The attack exploits the fact that when a victim clicks on the link and goes to the fake form they are not going to double-check the URL in the browser. After entering the credentials usually an attacker receives them in a separate email and the victim gets redirected to the original website.
This wonderful whitepaper dives deeper into the subject.
Phishing attack mitigation strategies
Currently the most effective mitigation against simple phishing attacks is Multi-Factor Authentication (MFA). Software-based MFAs such as temporary codes delivered in a separate message or Time-based One-Time Passwords (TOTP) can also be stolen, but require slightly more investment on the attackers front. Despite being only marginally harder to stage, those attacks take up only ~2% of the overall volume (needless to say this number is growing).
Man-in-the-middle phishing
Instead of hosting the impersonated login form separately an attacker can proxy the original website traffic. That allows the attacker to bypass the the second factor step. The approach works for bypassing email or SMS verification, TOTP, or even push. More sophisticated attacks can even proxy AJAX requests which makes the application fully functional after the victim signes up.
In a simple phishing attack the victim gets redirected to the real login form or a fake welcome page once the credentials have been stolen. At this point the victim might get very suspicious and they can realize they have been tricked. They kill all active sessions and reset the password kicking the attacker out.
When the real website is proxied the victim might not realize it is using a fake website and proceed using a it or even leave it. This is especially dangerous in case of typosquating. Imagine a situation where you type in your bank account website and make a typo. You login, check your balance and close the tab without even realizing your credentials just got stolen.
Man-in-the-middle phishing mitigation strategies
The only sure way to protect against a man-in-the-middle phishing attacks is to use a hardware MFA token based on public-key cryptography such as U2F or WebAuthn.
Conclusion
In the real scenarios the attacks described above are usually combined together to create so called hybrid password attacks. In further posts we can go in detail about how to put the defenses in place to help your users to stay safe. Let me know in the comments which attacks you want to explore further.